Millions of Americans own different types of mobile phones and all of these people know that fraudulent calls are already a huge problem in the US. It’s common for fraudsters to impersonate a trustworthy company in order to extract information from an individual or group of people. This is one of the reasons why 94% of people don’t answer phone calls unless they are certain where they came from.
The good news is that the Federal Communications Commission (FCC) has required that all telephone carriers adopt STIR/SHAKEN technology, which makes use of call authentication so the receiver can confidently identify a caller before picking up the phone. But, even though the adoption of STIR/SHAKEN does help identify callers, it doesn’t necessarily put an end to the illegal spoofing pandemic.
Below, we’ll define STIR/SHAKEN technology, what it means for businesses, and go over the additional steps that you have to take to protect your brand from being spoofed.
What is STIR/SHAKEN?
STIR/SHAKEN is a framework created to reduce robocalls by verifying the digital signature of an outbound call. Network providers are able to identify if a call is coming from a legitimate business or a scammer and label the call accordingly.
STIR stands for Secure Telephone Identity Revisited. STIR is a working group which has developed protocols used to create digital signatures for calls. SHAKEN stands for Secure Handling of Asserted Information Using Tokens. It is a standard that ensures STIR is being deployed by service providers.
Together, STIR/SHAKEN are standards and protocols used to implement call authentication over the IP network. Carriers declare the validity of caller IDs and monitor for corruption along the way. It is important to note that this framework helps detect fraudulent calls but does not prevent them. This means that your customers may still be suspicious of unidentified calls and, as a result, not answer the phone.
How does illegal call spoofing impact business?
Let’s take a look at the definition of illegal call spoofing.
When a spoofing attack occurs, it appears as if the call is coming from a location that is not its real source. In other words, call spoofing allows callers to mask their phone numbers and make it seem like their calls are originating from somewhere else. This practice is common among companies that outsource some of their operations overseas and businesses that have remote team members.
However, when callers spoof their numbers and use a company’s identity without authorization, it’s called illegal spoofing. And, even though this practice targets the people who receive the calls, it can have a detrimental effect on your company’s reputation. When your numbers are used for fraudulent purposes, customers are hesitant to trust your calls even when they are legitimate.
Are robocalls and spoofed calls the same thing?
Although both of them are extremely common, robocalls and spoofed calls are not exactly the same. Robocalls usually originate at a high volume through programmatic software and they can deliver a recording or open up interactions with live agents. These may sometimes be spoofed, but they need to come from dialing software to be considered robocalls.
Caller ID spoofing can be performed on any type of call, whether it’s generated by a dialing platform or manually. So, even though a robocall can be spoofed, it doesn’t mean that all of them are. Illegally spoofed calls are dangerous regardless of where they come from, which is one of the reasons why telecommunications companies have adopted STIR/SHAKEN protocols to ensure caller numbers aren’t spoofed illegally.
STIR/SHAKEN: The impact of VoIP and SIP technologies
Before going over STIR/SHAKEN technology and how it helps identify illegal call spoofing, let’s go over the impact of session initiation protocol (SIP) and voice over internet protocol (VoIP).
VoIP and SIP are two types of protocols that allow individuals to make calls through the internet, without having to connect to the public telephone grid. In the early stages of VoIP calls, different methods were employed by different proprietors.
SIP was later introduced as a standardized way to connect VoIP calls, but this technology also allowed calls to carry identification information by using simple headers. That said, SIP also gave callers the ability to edit this information, making it easier to spoof numbers and make it seem as if calls were originating from a different source.
How does STIR/SHAKEN work?
Now that we’ve covered the basics of VoIP, SIP, and illegal call spoofing, let’s discuss how STIR/SHAKEN technology works. As we mentioned previously, these are actually two types of technology, which stand for secure telephony identity revisited (STIR) and secure handling of asserted information using tokens (SHAKEN).
In simple terms, STIR technology allows for better caller identification because it verifies where the call is coming from at different points. Instead of actually preventing callers from changing their ID, it tells end users whether they should trust a call or not.
While STIR technology was developed to be compatible with VoIP calls, this system isn’t compatible with conventional telephone networks. This led to the development of SHAKEN, which serves a similar purpose to STIR but it’s compatible with telephone grids that don’t rely on internet connections.
Below, we’ve detailed what happens during each stage of a call when STIR/SHAKEN technology is implemented.
1. Invite Is received
When someone places a phone call, a SIP invite is sent to the carrier of the person or entity making the call. This is the very first step in the verification process and it’s important because it triggers a series of STIR/SHAKEN events designed to verify the identity of the caller.
2. Attestation level determination
When the telecommunications provider receives the invite from a caller, the company reviews the request before accepting it. Carriers need to verify the call source and the phone number being used to determine how to qualify the call. This is important because this data will also be relayed to the receiver’s network, even if it’s not the same as the caller’s.
The three levels of attestation in STIR/SHAKEN are full attestation, partial attestation, and gateway attestation, which are labeled as A, B, and C respectively in the network.
2.1 Full Attestation (A)
The best qualification you can get from STIR/SHAKEN is full attestation, which is represented with an A. This means that the telecommunications carrier has verified the identity of the caller and that the calling party has the authorization to use the number. A good example of this would be a member of the telecommunication provider’s softswitch.
2.2. Partial Attestation (B)
Partial attestation, which is represented by a B, is awarded when the carrier can verify that the call is coming from the location that appears on the STIR label. However, partial attestation also means that the carrier could not verify if the caller was authorized to use the number. This attestation is sometimes given to new company extensions that are not registered with the carrier.
2.3 Gateway Attestation (C)
Lastly, gateway attestation is given when the carrier was able to verify where it received the call from, but not its original location. Gateway attestation, which appears as a C on the receiver’s device, is usually given to international calls, but it can also be a red flag if the number is local.
3. Identity header creation
Once attestation has been awarded and a phone call is properly verified, the carrier creates a SIP header that contains identity information. Keep in mind that the verification platform integration can come from a third-party provider that specializes in connecting to carrier softwitches.
The identity header includes data like caller number, basic call history, timestamp, attestation grading, and origination identifier.
4. Token verification
Once the identity header is created, your call is ready to be sent out. Remember, all this process occurs in a matter of seconds, so you need to ensure that your SIP header contains the right information.
In the next step, the caller’s carrier sends out the SIP invite and identity header information to the receiver’s phone service provider. In some cases, the identity token is also sent to the call placement service of the receiver’s telecommunications company. This is an additional precaution that helps avoid tampering and improved data accuracy.
5. Verification Initiation
Once the receiver’s carrier gets the invite request and header information, they pass it on to the verification service. Remember, the verification service can be an in-house solution or a cloud-hosted third-party service, but the process takes seconds none-the-less.
6. Certificate Reception and Authentication
When the verification service receives an authentication request, it performs multiple checks in order to ensure that the call is not spoofed. During this step, the verification service provider pulls the digital certificate from the caller’s carrier and begins performing different tests. If all verification steps are passed properly, the call was not spoofed.
In this step, the carrier’s verification service on the receiver’s end can check things like the identity header, the validity of the SIP signature through public keys, and the certificate chain of trust.
7. Final Verification and Call Connection
Finally, the verification process returns its results to the carrier. If the result is successful and the call was not spoofed, the call is passed on to the receiving carrier’s softswitch. If the process is completed and it seems like a call has been spoofed, it’s sent to the receiver along with a warning that it may be spoofed.
Does STIR/SHAKEN eliminate illegal call spoofing?
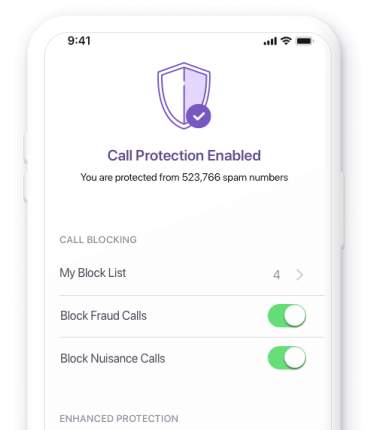
While STIR/SHAKEN technology does unveil illegal call spoofing, it doesn’t stop it or reduce the number of times it actually occurs. If you want to take full control of what happens to calls that are illegally spoofing your company numbers, Hiya connect Secure Call can help you do exactly that. Through Hiya Connect, you can choose whether the call is simply unveiled, blocked, or labeled as spoofed when the caller receives it.
Interested in the impact Hiya Connect can have on your business? Download the Forrester Consulting Total Economic Impact™ Study commissioned by Hiya.